I have written on�WordPress�security in the past and listed some plugins that cover popular security issues. I have used Simple Login log in the past, and it is quite good although no longer good enough solution to secure WordPress admin area alone.
Typical solution will block admin folder only and maybe wp-login. This is no longer good enough, as it will not prevent someone from using login page to brute-forcing your password. As I have found out the hard way, this might cause serious problems.�
Using .htaccess to secure WordPress admin and other areas
Recently, one of my WP blog servers had connection problems. They were caused by someone trying to guess admin user’s password couple tries per second. Simple Login Log tracks such things and increases the load even further (as it writes such entries to db). This was complicated further by spam bots (I get around 2500 spam comments per day on that blog).
So, how to �prevent this from happening, preferably on all blogs hosted on the same server?
Interestingly, you can add allow/deny directives for single file (or group of files) as well, and they work on server-basis if added in the main config file (/etc/httpd/conf.d/httpd.conf in my case).
The rules look like this :
<files wp-login.php>
Order Deny,Allow
Deny from All
allow from xxx.xxx
allow from xxx.xxx.xxx.xxx
</files>
There are 2 ways to white-list IPs.
XXX.XXX or XXX.XXX.XXX – subnet where you login from without fixed IPs,
and xxx.xxx.xxx.xxx are ip you login from.
Now each attempt to brute-force your password into your WordPress admin it will result in adding 2 lines to log files : one to access log and one to error log. It will not be processed by PHP.
Another part to whitelist-only is XML-RPC backend on wordpress (xml-rpc.php). It is used for remote administration, but you should not leave it open in most of the cases as it allows brute-forcing passwords. You can include it under similar rule in global config file. This increases security of your wordpress admin and reduces server load.
Using global config to block bad commenters
Additionally, one could use this way to block some popular (Chineese mostly) spam bot IPs:
<Files wp-comments-post.php>
Order Allow,Deny
allow from all
deny from 113.212.70
deny from 123.156
deny from 218.72
deny from 60.182.158
</Files>
We write out bad ips and networks here.�
�
Using IP Geo Block to block bad visitors
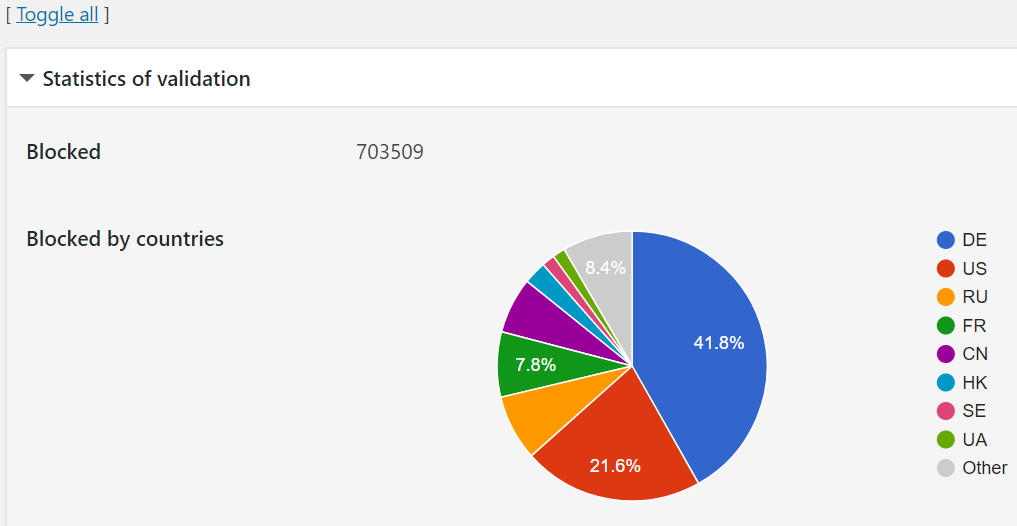
On many sites I use IP Geo Block currently to secure WordPress admin. It blocks separate areas by using GEO IP databases that it downloads to the wordpress servers.
Why this is useful ? Well, it is better in some cases than global blacklist list due to following:
- It refreshes list of IPs by countries regularly, thus you don’t need to maintain it
- It blocks against some common exploits as well.
- It blocks IP’s access to wp-login or xml-rpc after some bad tries. This secures WordPress admin dashboard even from attacks from the same network (if you IP is dynamic, you might have to use this).
- It keeps logs if you wish and you can turn them off if you have too many attacks.�
It is great solution to prevent some location-based spam and attack bots, though it is not suitable to block non-location based networks from access commenting.


0 Comments