Several botnets were shut down and the CEO of rogue parmacy and fake antivirus credit card processor was arrested recently. This resulted in the significant drop of malicious software activity in August. Many took time to celebrate and rightfully so. However, I do not think this is the end of Fake AVs or malware in general.
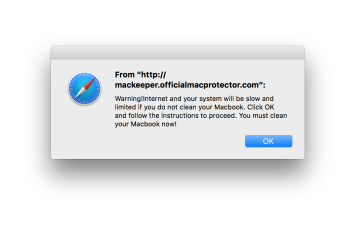
First, some background. The days of malware made by computer nerds for fun are long gone. The most of malware is created for profit, and as long as you see something on your PC, you can safely assume that it is for profiting. Fake AVs are best known and annoying nowadays as they collected payments directly by asking to pay for non-existing full version. To make you pay, they scare you with non-existing threats for your PC. There were some variations with this, like recent PC Repair malware that scares with hardware errors instead of viruses, but the way they collect payment is the same: They ask for you to pay directly.
These payments cannot be processed easily, as every bank, Visa and Master Card looks for scams. Thus payment gateways are major bottleneck and risk point for malware makers. And taking even single of them down (not the website, but the company itself) hurts each of them significantly. Differently from malware skins and websites, it is more complex and costly task.
So, what will happen once the payment gateway gets down? There are many ways malware makers can still make money, and our experience shows that they do exactly that.
For example, we see a rise of clickjacking attacks, which forces user to click on their affiliated links that might not be harmful per se. The user is redirected from “real” websites or search results to the websites malware makers insert. The owners pay malware makers for traffic or sales. Some of them are innocent, some just do not care about the source of the traffic. The famous google redirect virus, though there are other implementations as well.
Another possible way to make money for malware makers is distributing legal anti-malware or anti-virus programs instead of fake ones. This is illegal according to affiliate guidelines of all legitimate affiliate networks, but they might hope not to be caught. While there are various opinions which software is more likely to be distributed illegally, I would say this is not important at all. This can happen and will happen with all legitimate malware removal programs. We have seen such things in the past as well.
Thirdly, one could spice up things with using other, non-security related programs that will require payment. This is already happening with VLC, which “paid version” is distributed by malware makers. There are affiliate programs for various codec packs as well, which are distributed by malware makers.
And lastly, they could return to adware or spyware model of operation, which pays less than others, but has less risks as well.
Thus it is highly obvious that we will not see less infections in the long run. What we see is the result of both some security program makers and PC owners focusing on visible forms of malware and judging amount of infections from that.



0 Comments